OSWP: WiFu Review
OSWP (Offensive Security Wireless Professional) is a wireless hacking certification earned upon completion of Offensive Security's WiFu course.
The course consists of a 380 page book full of practical exercises, instructional videos, and an exam. You require hardware to complete the exercises: A card that supports injection and a home router with wireless capabilities. One must schedule the exam within 120 days after starting the course.
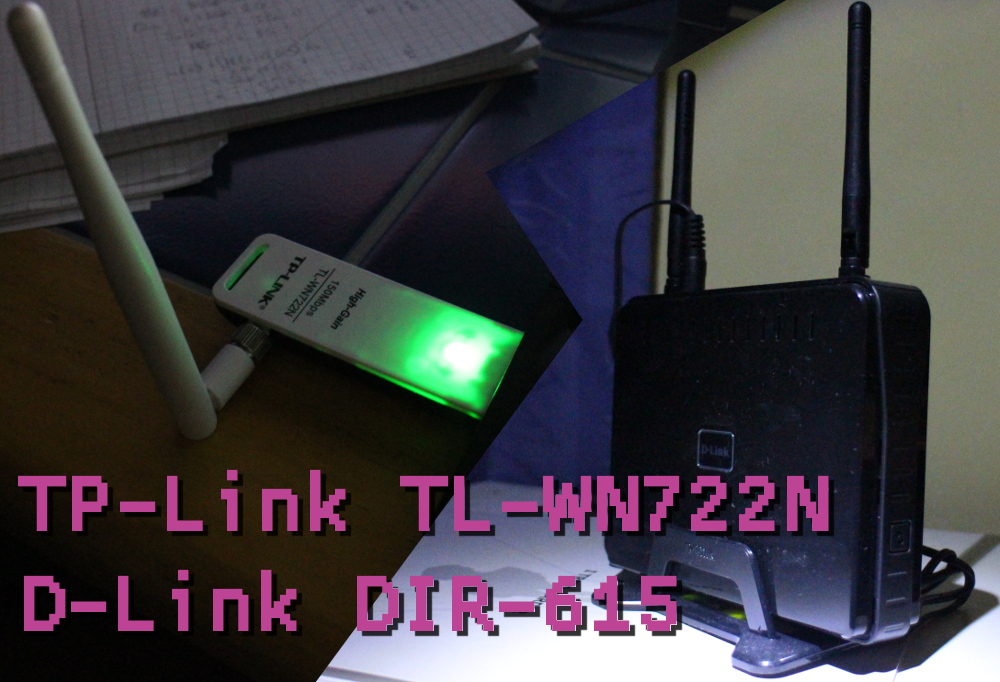
0. The Hardware
I used a TP-Link TL-WN722N and a D-Link DIR-615, setting me back about €40 including shipping. You can probably use your current card and WiFi - assuming repeatedly changing the WiFi settings wouldn't enrage other users and you are careful not to send anything sensitive while the network is vulnerable to sniffing. See here to check if your card is compatible with aircrack-ng.
1. The Book and its Exercises
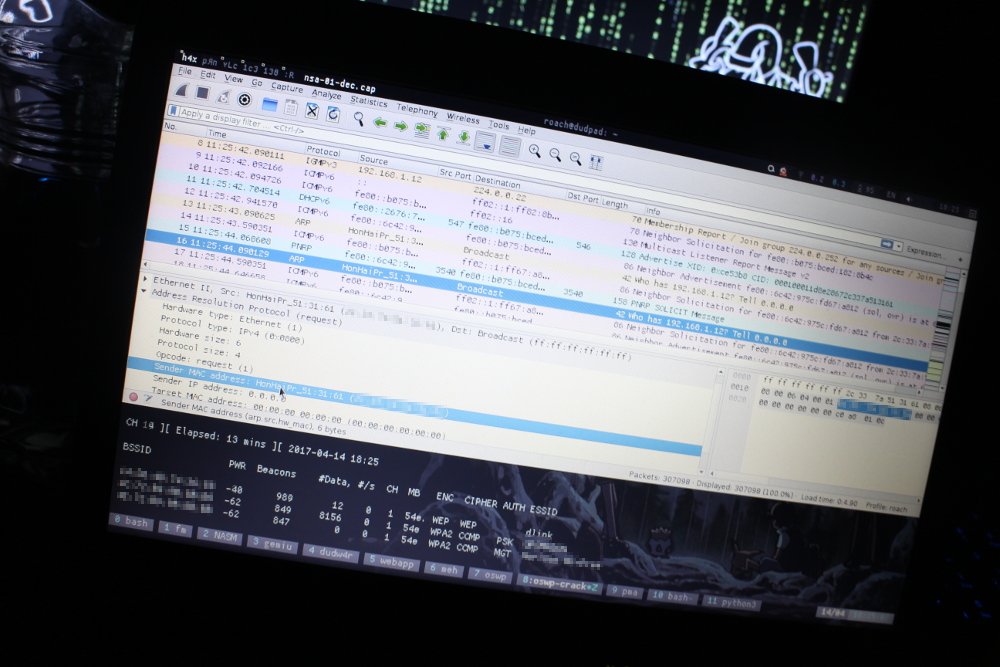
The book is partially designed by the author of aircrack-ng, which is a software suite the student becomes very familiar with. The first third of the book is quite dry theory - no exercises beyond packet inspection. Still, it was designed this way for a reason. Understanding 802.11 packets and WiFi procedures (beacon/probe/association/auth/encryption...) in detail provides an ideal framework for understanding the attacks.
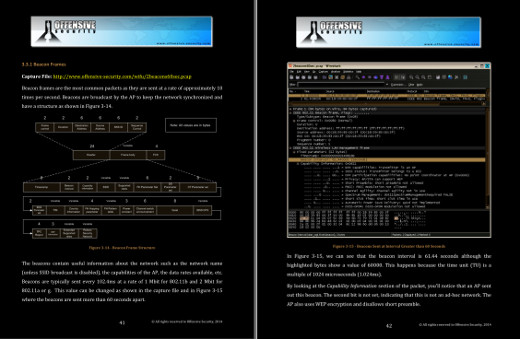
After that, every chapter has serveral exercises. Where one sets up one's wireless network in a specific way and then performs the attack detailed earlier in the chapter. They are all interesting and well worth doing. Little nuances, like capturing the wrong packet when you want to repeat ARP requests, are far more easily understood by getting your hands dirty.
Towards the end of the book we get a taste of some of the more interesting sorts of attacks. Like using your wireless card as a fake AP, forwarding that connection to your wired internet connection, and then running MITM attacks on anyone who connects. Or like wardriving.
I did not make much use of the videos except for the section on Kismet, but they seemed succinct and well planned.
2. The Exam
Although Offensive Security does not release exam success/failure rates, I would not be surprised if OSWP is far more frequently passed than OSCP. There is much taught in the book that would be impractical to test and as such one can be pretty confident it only requires a few techniques.
The exam itself is 4 hours, you SSH into a machine (you don't need your hardware for it) and after that you have 24 hours to submit your report. If you successfully complete every exercise lab in the book, the exam should be no problem.
3. Was it worth it?
After the time spent doing it and the price (about €500 including hardware), is it worth it?
From a savvy employer's point of view, it is nothing compared to OSCP. The simplicity of the exam itself also lowers its capability of putting you ahead of others. That said, it is obviously not nothing and I'm much more glad to have it beside my name than other popular certs.
What shines in this course is the practical value of the techniques - and just how interesting it all is! Nothing gives you an appreciation for how insecure certain protocols are when you can sniff and decrypt every packet in the air. Since the advents of switches (as opposed to hubs) promiscuous mode does not do much on wired networks. Wirelessly, it's all available. All this is especially useful if you are like I was and did not know much about the wireless world or level 2 frames in general.
Was it worth it for me?
Yes, absolutely! If a course can make you think digitally and specifically about the electromagnetic field around you in such a way that anyone close could be DoS'd with plausible deniability, have their traffic sniffed and possibly decrypted, or even worse - man in the middle attacked. Gives just a little more emphasis to making a long WPA password.
↑ Top ⌂ Home